An integrated software suite for connecting security systems, processes and teams
Security Organizations using SureViews Operations SaaS suite process events quickly, consistently, and securely: delivering better security outcomes

Simplify Security Operations
An integrated software suite for connecting security systems, processes and teams
Security Organizations using SureViews Operations SaaS suite process events, quickly, consistently and securely, delivering better security outcomes
A Suite of Modules for Any Security Team
A Suite of Modules for Any Security Team
SureView Operations is a PSIM delivered as a SaaS that offers a suite of software to simplify and improve the management of physical security programs. You can subscribe to individual modules or the entire suite for dramatically enhanced security operations.
SureView Operations is a PSIM delivered as a SaaS that offers a suite of software to simplify and improve the management of physical security programs. You can subscribe to individual modules or the entire suite for dramatically enhanced security operations.
 Response
Response
A single interface for coordinating the real-time response to alarms and events
 Field Operations
Field Operations
Connect your field team seamlessly with the command center and track your critical assets
 Cases
Cases
The flexible incident-tracking and investigation tool that adapts to your workflow
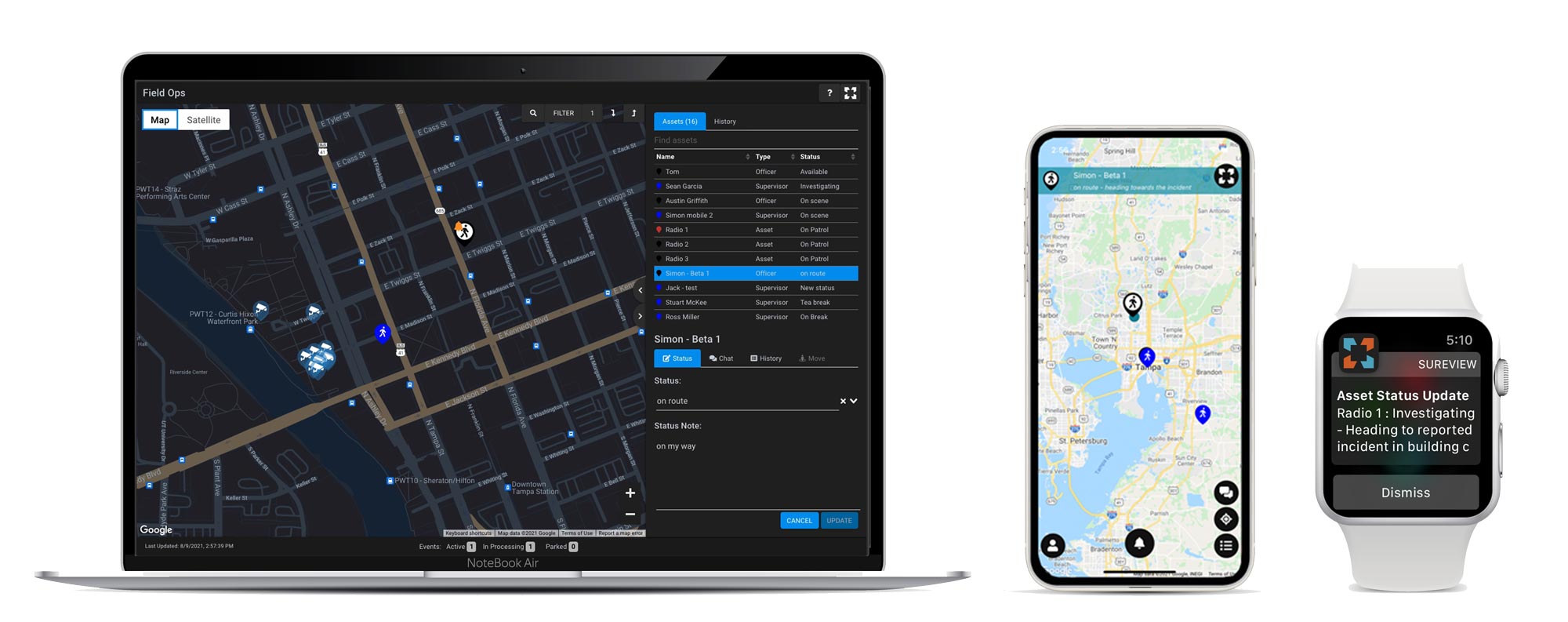
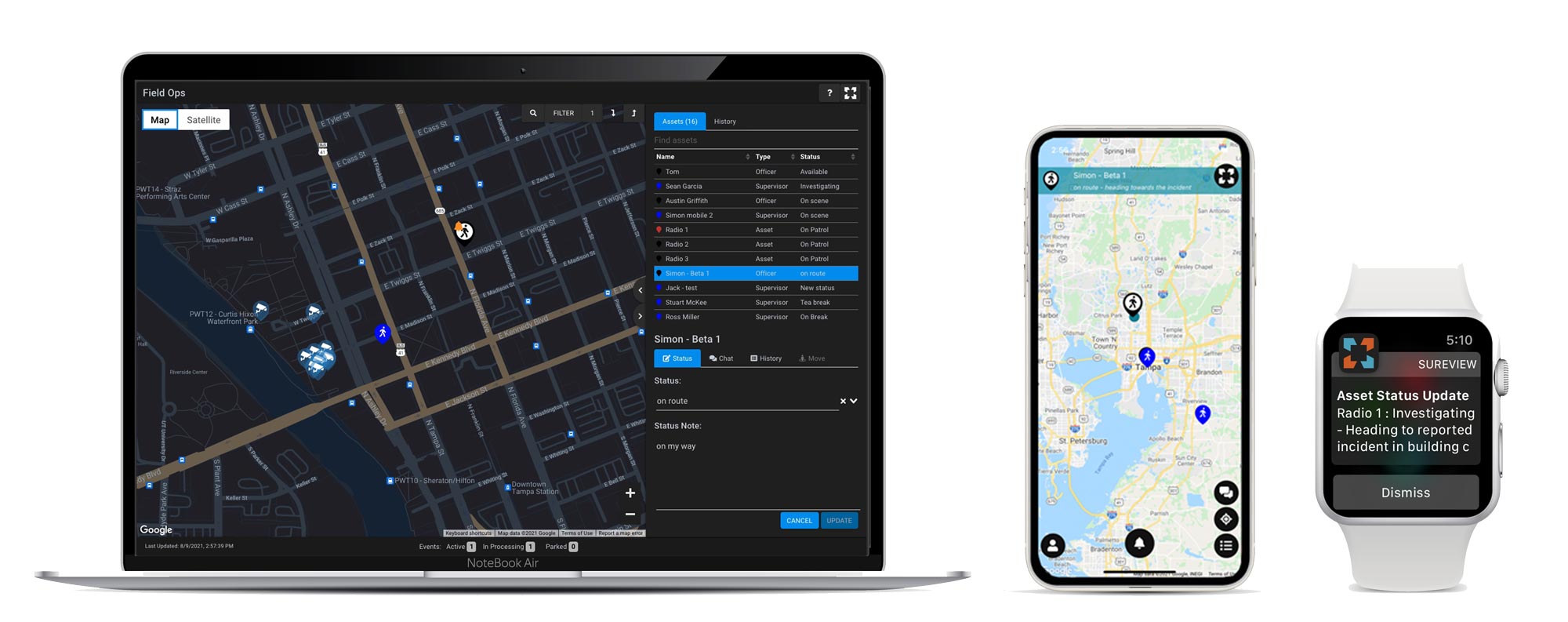
 Field Operations
Field Operations
Connect your field team seamlessly with the command center and track your critical assets
Learn More
 Response
Response
SureView provides a single screen to coordinate every alarm and event that comes into your SOC (Security Operations Center)—from any system, any device, any source. Everything needed for efficient response is right there—geospatial mapping, action plans, nearby cameras, call lists, etc. Alarms are automatically grouped and prioritized so operators receive the urgent ones first. No more jumping from one system to another, every event is handled in a similar, consistent way, driving productivity and improving security outcomes.
- » Single interface for response
- » Alarms from any source
- » Enforce policies with customizable Action Plans
- » Centralized Reporting and Analysis. Take action by making Data-driven Decision
- » Improve situational awareness:
- › Geospatial mapping
- › Stream cameras nearest event

 Field Operations
Field Operations
SureView’s Field Operations tool seamlessly connects your teams in the SOC and the field–providing real-time location and status information about field staff and critical assets. Field Operations also provides the situational awareness everyone on the team needs to effectively respond to events. Using the Mobile app, field staff can send and receive notifications of important incidents and status changes and share video, photos, and notes back and forth with operations. With the touch of a button, Operators can bring key stakeholders into any event.
- » Instant communication between SOC and field teams
- » Mobile App tracks the real-time location of the team
- » Quickly identify the nearest available team member to the event
- » Notification for critical alarms, status changes, and real-time communication
- » Track location and status of key assets
- » Keep key stakeholders informed
 Field Operations
Field Operations
SureView’s Field Operations tool seamlessly connects your teams in the SOC and the field–providing real-time location and status information about field staff and critical assets. Field Operations also provides the situational awareness everyone on the team needs to effectively respond to events. Using the Mobile app, field staff can send and receive notifications of important incidents and status changes and share video, photos, and notes back and forth with operations. With the touch of a button, Operators can bring key stakeholders into any event.
- » Instant communication between SOC and field teams
- » Mobile App tracks the real-time location of the team
- » Quickly identify the nearest available team member to the event
- » Notification for critical alarms, status changes, and real-time communication
- » Track location and status of key assets
- » Keep key stakeholders informed
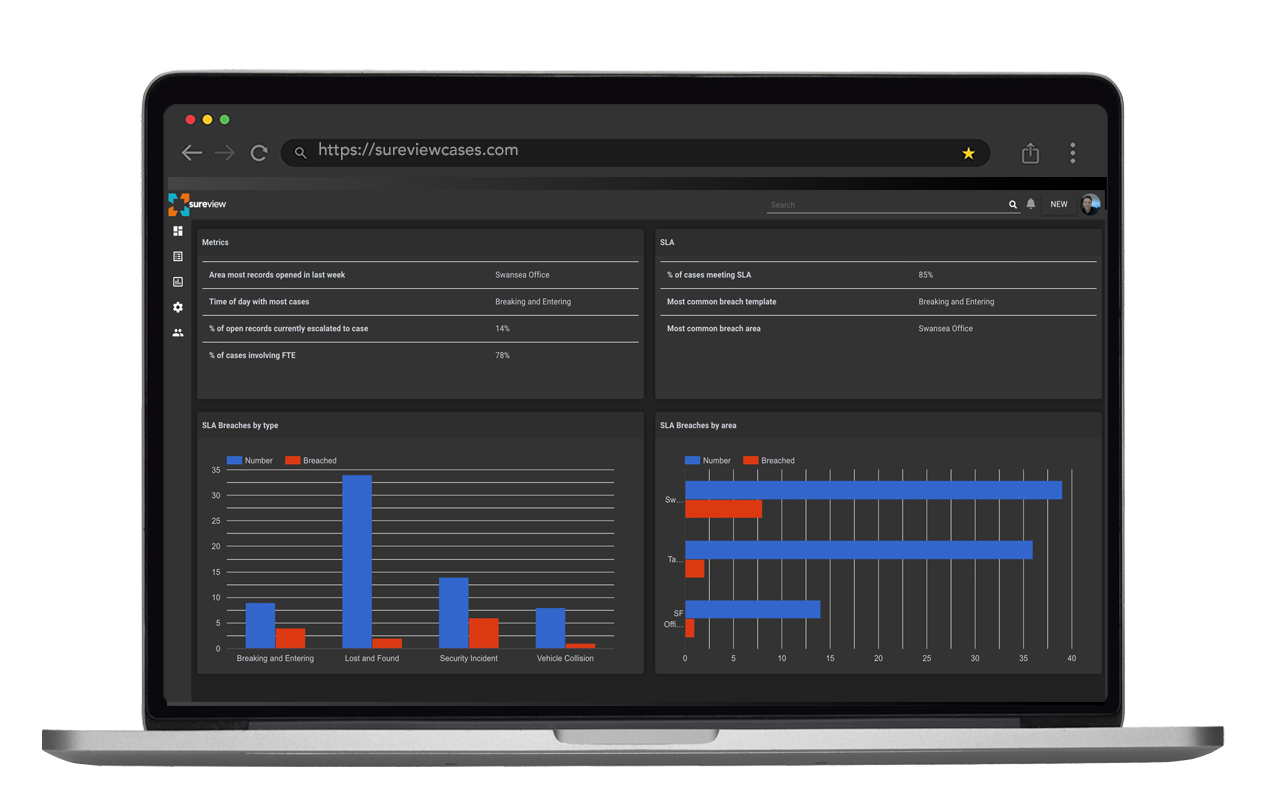
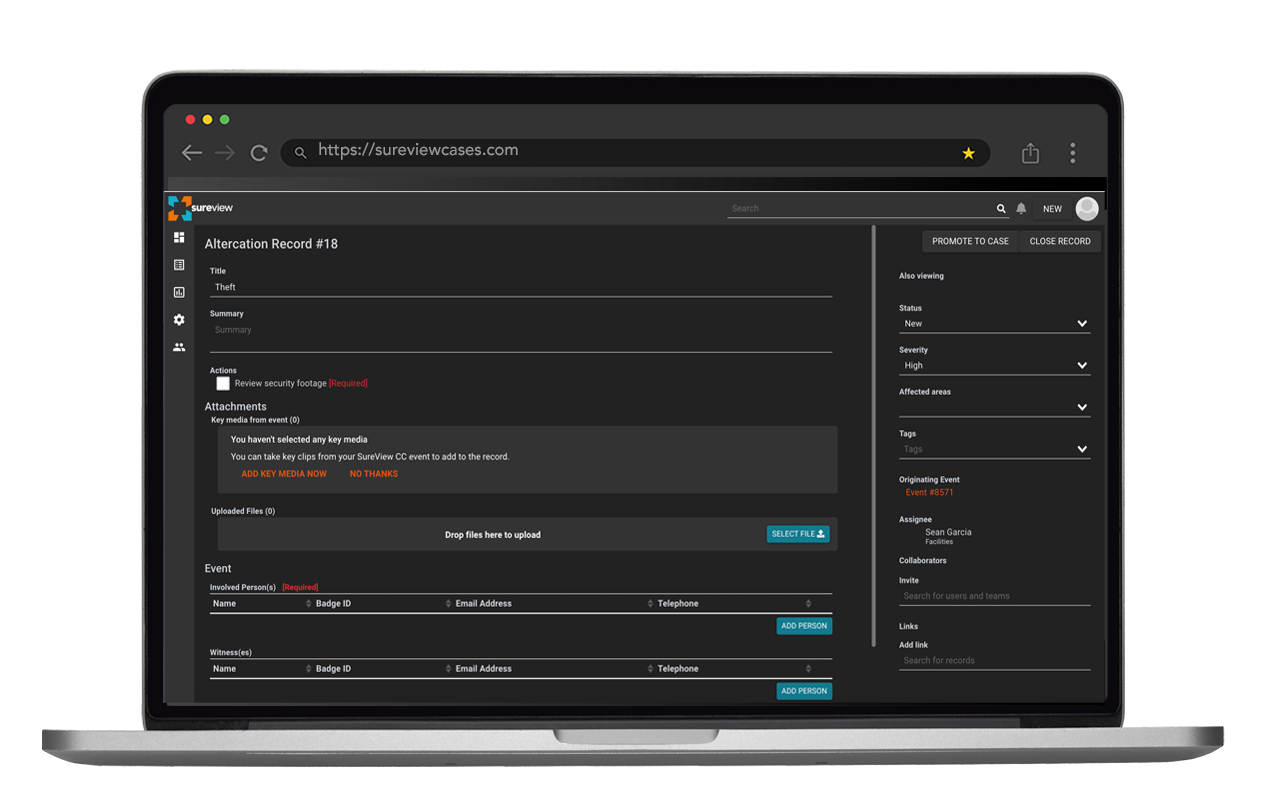
 Cases
Cases
Cases is SureView’s open incident tracking and investigation tool. It’s designed to audit and automate record-keeping and compliance and seamlessly deliver information from operations to investigations teams—immediately, succinctly, accurately. Whether your team is triaging an event or investigating afterwards, the information is right there —from recording the comings and goings of your vehicle fleet, to lost-and-found, to more serious incidents such as an injury or assault. With the flexibility to create your own workflows, Cases is designed to meet the needs of any organization.
- » Connect SOC Operations and Investigations teams
- » Flexible design adapts to any organization or workflow
- » Open API to share data with enterprise back office systems
- » Automate compliance and reporting
 Cases
Cases
Cases is SureView’s open incident tracking and investigation tool. It’s designed to audit and automate record-keeping and compliance and seamlessly deliver information from operations to investigations teams—immediately, succinctly, accurately. Whether your team is triaging an event or investigating afterwards, the information is right there —from recording the comings and goings of your vehicle fleet, to lost-and-found, to more serious incidents such as an injury or assault. With the flexibility to create your own workflows, Cases is designed to meet the needs of any organization.
- » Connect SOC Operations and Investigations teams
- » Flexible design adapts to any organization or workflow
- » Open API to share data with enterprise back office systems
- » Automate compliance and reporting
Integrated with the tools you rely on
Whether its leveraging universal protocols or native plugins from our library, SureView next-gen PSIM simplifies the integration with your security operations and the back-office systems of your organization
Integrated with the tools you rely on
Whether its leveraging universal protocols or native plugins from our library, SureView next-gen PSIM simplifies the integration with your security operations and the back-office systems of your organization

WE HELP CUSTOMERS :
- Manage scale and complexity
- Embrace new technology
- Rapidly deploy with SaaS
- Speed up response
- Integrate multiple systems


Learn More?
Want to learn more about what we do? Speak with an engineer? See SureView in action? Coordinate a reference call? Please choose a time straight from our calendar.
Or, further explore our case studies, products, blog or download a white paper


Want to learn more about what we do? Speak with an engineer? See SureView in action? Coordinate a reference call? Please choose a time straight from our calendar.
Or, further explore our case studies, products, blog or download a white paper


 Simplify Security Operations
Simplify Security Operations  Field Operations
Field Operations Cases
Cases